CDH 10Cloudera Manager Kerberos安装配置CA配置(markdown新版三)
文章目录
- 一、配置证书节点(所有节点单独执行)
- 1、创建目录存放证书
- 2、生成 Java keystore
- 3、生成java keystore证书签名(certificate signing request CSR)
- 4、各节点生成csr文件发送到cdh-cm-v01搭建的CA服务器上
- 5、将CSR生成证书
- 1)cdh-cm-v01节点CSR生成操作
- 2)其它节点CSR生成操作
- 3)最终查询结果
- 6、将SRC certificate发送回对应的节点
- 7、验证(所有节点)
- 8、拷贝CA certificates到所有节点,并重命名
- 1)拷贝root CA certificates到所有节点,并重命名为rootca.pem
- 2)拷贝intermediate CA certificates到所有节点,并重命名为intca.pem
- 9、将JDK的cacerts文件拷贝到jssecacerts
- 10、将root CA certificate导入到jssecacerts当中(所有机器)
- 11、将intermediate CA certificate添加到各节点的节点证书中,并将其导入到java keystore中
- 12、创建软连接(所有机器)
- 13、创建软连接(cdh-cm-v01)
一、配置证书节点(所有节点单独执行)
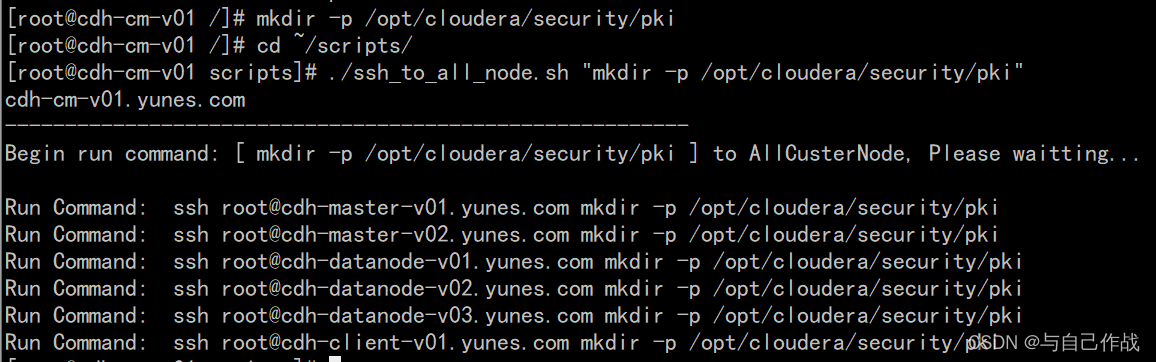
1、创建目录存放证书
mkdir -p /opt/cloudera/security/pki
cd ~/scripts/;
sh ./ssh_to_all_node.sh “mkdir -p /opt/cloudera/security/pki”
[root@cdh-cm-v01 /]# mkdir -p /opt/cloudera/security/pki
[root@cdh-cm-v01 /]# cd ~/scripts/
[root@cdh-cm-v01 scripts]# ./ssh_to_all_node.sh "mkdir -p /opt/cloudera/security/pki"
cdh-cm-v01.yunes.com
---------------------------------------------------------
Begin run command: [ mkdir -p /opt/cloudera/security/pki ] to AllCusterNode, Please waitting...
Run Command: ssh root@cdh-master-v01.yunes.com mkdir -p /opt/cloudera/security/pki
Run Command: ssh root@cdh-master-v02.yunes.com mkdir -p /opt/cloudera/security/pki
Run Command: ssh root@cdh-datanode-v01.yunes.com mkdir -p /opt/cloudera/security/pki
Run Command: ssh root@cdh-datanode-v02.yunes.com mkdir -p /opt/cloudera/security/pki
Run Command: ssh root@cdh-datanode-v03.yunes.com mkdir -p /opt/cloudera/security/pki
Run Command: ssh root@cdh-client-v01.yunes.com mkdir -p /opt/cloudera/security/pki
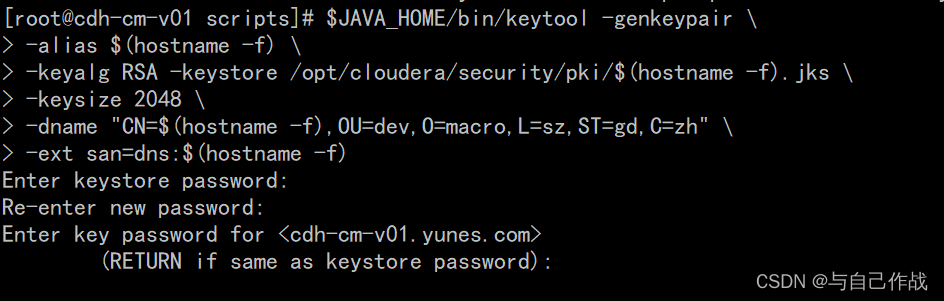
2、生成 Java keystore
$JAVA_HOME/bin/keytool -genkeypair
-alias ( h o s t n a m e − f ) − k e y a l g R S A − k e y s t o r e / o p t / c l o u d e r a / s e c u r i t y / p k i / (hostname -f) \ -keyalg RSA -keystore /opt/cloudera/security/pki/ (hostname−f) −keyalgRSA−keystore/opt/cloudera/security/pki/(hostname -f).jks
-keysize 2048
-dname "CN= ( h o s t n a m e − f ) , O U = d e v , O = m a c r o , L = s z , S T = g d , C = z h " − e x t s a n = d n s : (hostname -f),OU=dev,O=macro,L=sz,ST=gd,C=zh" \ -ext san=dns: (hostname−f),OU=dev,O=macro,L=sz,ST=gd,C=zh" −extsan=dns:(hostname -f)
[root@cdh-cm-v01 scripts]# $JAVA_HOME/bin/keytool -genkeypair \
> -alias $(hostname -f) \
> -keyalg RSA -keystore /opt/cloudera/security/pki/$(hostname -f).jks \
> -keysize 2048 \
> -dname "CN=$(hostname -f),OU=dev,O=macro,L=sz,ST=gd,C=zh" \
> -ext san=dns:$(hostname -f)
Enter keystore password: tianlingqun
Re-enter new password: tianlingqun
Enter key password for <cdh-cm-v01.yunes.com>
(RETURN if same as keystore password):
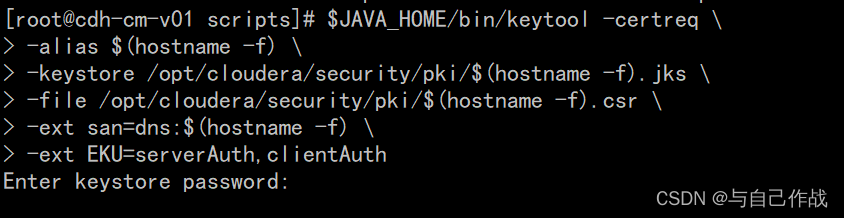
3、生成java keystore证书签名(certificate signing request CSR)
$JAVA_HOME/bin/keytool -certreq
-alias ( h o s t n a m e − f ) − k e y s t o r e / o p t / c l o u d e r a / s e c u r i t y / p k i / (hostname -f) \ -keystore /opt/cloudera/security/pki/ (hostname−f) −keystore/opt/cloudera/security/pki/(hostname -f).jks
-file /opt/cloudera/security/pki/ ( h o s t n a m e − f ) . c s r − e x t s a n = d n s : (hostname -f).csr \ -ext san=dns: (hostname−f).csr −extsan=dns:(hostname -f)
-ext EKU=serverAuth,clientAuth
[root@cdh-cm-v01 scripts]# $JAVA_HOME/bin/keytool -certreq \
> -alias $(hostname -f) \
> -keystore /opt/cloudera/security/pki/$(hostname -f).jks \
> -file /opt/cloudera/security/pki/$(hostname -f).csr \
> -ext san=dns:$(hostname -f) \
> -ext EKU=serverAuth,clientAuth
Enter keystore password: tianlingqun
4、各节点生成csr文件发送到cdh-cm-v01搭建的CA服务器上
host_name=cdh-master-v01.yunes.com; scp -P36565 root@ h o s t n a m e : / o p t / c l o u d e r a / s e c u r i t y / p k i / {host_name}:/opt/cloudera/security/pki/ hostname:/opt/cloudera/security/pki/{host_name}.csr /root/ca/intermediate/csr/
host_name=cdh-master-v02.yunes.com; scp -P36565 root@ h o s t n a m e : / o p t / c l o u d e r a / s e c u r i t y / p k i / {host_name}:/opt/cloudera/security/pki/ hostname:/opt/cloudera/security/pki/{host_name}.csr /root/ca/intermediate/csr/
host_name=cdh-client-v01.yunes.com; scp -P36565 root@ h o s t n a m e : / o p t / c l o u d e r a / s e c u r i t y / p k i / {host_name}:/opt/cloudera/security/pki/ hostname:/opt/cloudera/security/pki/{host_name}.csr /root/ca/intermediate/csr/
host_name=cdh-datanode-v01.yunes.com; scp -P36565 root@ h o s t n a m e : / o p t / c l o u d e r a / s e c u r i t y / p k i / {host_name}:/opt/cloudera/security/pki/ hostname:/opt/cloudera/security/pki/{host_name}.csr /root/ca/intermediate/csr/
host_name=cdh-datanode-v02.yunes.com; scp -P36565 root@ h o s t n a m e : / o p t / c l o u d e r a / s e c u r i t y / p k i / {host_name}:/opt/cloudera/security/pki/ hostname:/opt/cloudera/security/pki/{host_name}.csr /root/ca/intermediate/csr/
host_name=cdh-datanode-v03.yunes.com; scp -P36565 root@ h o s t n a m e : / o p t / c l o u d e r a / s e c u r i t y / p k i / {host_name}:/opt/cloudera/security/pki/ hostname:/opt/cloudera/security/pki/{host_name}.csr /root/ca/intermediate/csr/
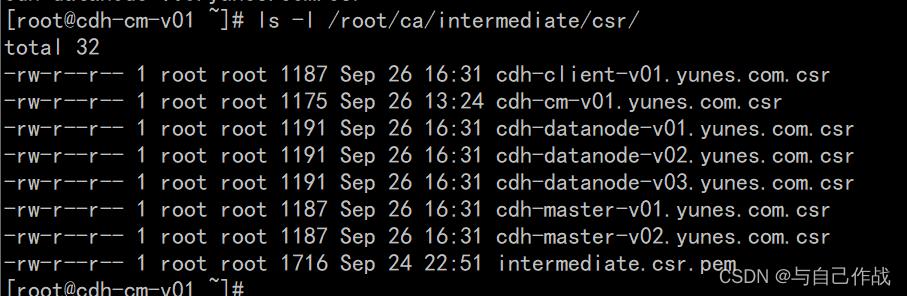
ls -l /root/ca/intermediate/csr/
[root@cdh-cm-v01 ~]# host_name=cdh-master-v01.yunes.com; scp -P36565 root@${host_name}:/opt/cloudera/security/pki/${host_name}.csr /root/ca/intermediate/csr/
host_name=cdh-master-v02.yunes.com; scp -P36565 root@${host_name}:/opt/cloudera/security/pki/${host_name}.csr /root/ca/intermediate/csr/
host_name=cdh-client-v01.yunes.com; scp -P36565 root@${host_name}:/opt/cloudera/security/pki/${host_name}.csr /root/ca/intermediate/csr/
host_name=cdh-datanode-v01.yunes.com; scp -P36565 root@${host_name}:/opt/cloudera/security/pki/${host_name}.csr /root/ca/intermediate/csr/
host_name=cdh-datanode-v02.yunes.com; scp -P36565 root@${host_name}:/opt/cloudera/security/pki/${host_name}.csr /root/ca/intermediate/csr/
cdh-master-v01.yunes.com.csr 100% 1187 210.6KB/s 00:00
[root@cdh-cm-v01 ~]# host_name=cdh-master-v02.yunes.com; scp -P36565 root@${host_name}:/opt/cloudera/security/pki/${host_name}.csr /root/ca/intermediate/csr/
cdh-master-v02.yunes.com.csr 100% 1187 1.7MB/s 00:00
[root@cdh-cm-v01 ~]# host_name=cdh-client-v01.yunes.com; scp -P36565 root@${host_name}:/opt/cloudera/security/pki/${host_name}.csr /root/ca/intermediate/csr/
cdh-client-v01.yunes.com.csr 100% 1187 1.4MB/s 00:00
[root@cdh-cm-v01 ~]# host_name=cdh-datanode-v01.yunes.com; scp -P36565 root@${host_name}:/opt/cloudera/security/pki/${host_name}.csr /root/ca/intermediate/csr/
cdh-datanode-v01.yunes.com.csr 100% 1191 1.2MB/s 00:00
[root@cdh-cm-v01 ~]# host_name=cdh-datanode-v02.yunes.com; scp -P36565 root@${host_name}:/opt/cloudera/security/pki/${host_name}.csr /root/ca/intermediate/csr/
cdh-datanode-v02.yunes.com.csr 100% 1191 1.5MB/s 00:00
[root@cdh-cm-v01 ~]# host_name=cdh-datanode-v03.yunes.com; scp -P36565 root@${host_name}:/opt/cloudera/security/pki/${host_name}.csr /root/ca/intermediate/csr/
cdh-datanode-v03.yunes.com.csr
[root@cdh-cm-v01 ~]# ls -l /root/ca/intermediate/csr/
total 32
-rw-r--r-- 1 root root 1187 Sep 26 16:31 cdh-client-v01.yunes.com.csr
-rw-r--r-- 1 root root 1175 Sep 26 13:24 cdh-cm-v01.yunes.com.csr
-rw-r--r-- 1 root root 1191 Sep 26 16:31 cdh-datanode-v01.yunes.com.csr
-rw-r--r-- 1 root root 1191 Sep 26 16:31 cdh-datanode-v02.yunes.com.csr
-rw-r--r-- 1 root root 1191 Sep 26 16:31 cdh-datanode-v03.yunes.com.csr
-rw-r--r-- 1 root root 1187 Sep 26 16:31 cdh-master-v01.yunes.com.csr
-rw-r--r-- 1 root root 1187 Sep 26 16:31 cdh-master-v02.yunes.com.csr
-rw-r--r-- 1 root root 1716 Sep 24 22:51 intermediate.csr.pem
5、将CSR生成证书
1)cdh-cm-v01节点CSR生成操作
vi /root/ca/intermediate/openssl.cnf
host_name=cdh-cm-v01.yunes.com
openssl ca -config /root/ca/intermediate/openssl.cnf
-extensions server_cert
-days 3600
-notext
-in /root/ca/intermediate/csr/ h o s t n a m e . c s r − o u t / r o o t / c a / i n t e r m e d i a t e / c e r t s / {host_name}.csr \ -out /root/ca/intermediate/certs/ hostname.csr −out/root/ca/intermediate/certs/{host_name}.pem
[root@cdh-cm-v01 ~]# host_name=cdh-cm-v01.yunes.com
[root@cdh-cm-v01 ~]# openssl ca -config /root/ca/intermediate/openssl.cnf \
> -extensions server_cert \
> -days 3600 \
> -notext \
> -in /root/ca/intermediate/csr/${host_name}.csr \
> -out /root/ca/intermediate/certs/${host_name}.pem
Using configuration from /root/ca/intermediate/openssl.cnf
Enter pass phrase for /root/ca/intermediate/private/intermediate.key.pem: tianlingqun
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number: 4096 (0x1000)
Validity
Not Before: Sep 26 10:19:05 2022 GMT
Not After : Aug 4 10:19:05 2032 GMT
Subject:
countryName = zh
stateOrProvinceName = gd
localityName = sz
organizationName = macro
organizationalUnitName = dev
commonName = cdh-cm-v01.yunes.com
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Cert Type:
SSL Client, SSL Server
Netscape Comment:
OpenSSL Generated Server Certificate
X509v3 Subject Key Identifier:
01:81:D5:42:5D:F5:1D:8E:67:CC:C3:34:29:8F:5D:5E:57:90:25:FC
X509v3 Authority Key Identifier:
keyid:AC:52:5E:07:72:71:85:56:01:CF:53:1F:5A:60:A4:1B:82:F4:6B:F1
DirName:/C=zh/ST=gd/L=sz/O=yunes/OU=yunes/CN=yunes/emailAddress=gsxxx@163.com
serial:10:00
X509v3 Key Usage: critical
Digital Signature, Key Encipherment
X509v3 Extended Key Usage:
TLS Web Server Authentication, TLS Web Client Authentication
Certificate is to be certified until Aug 4 10:19:05 2032 GMT (3600 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified, commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
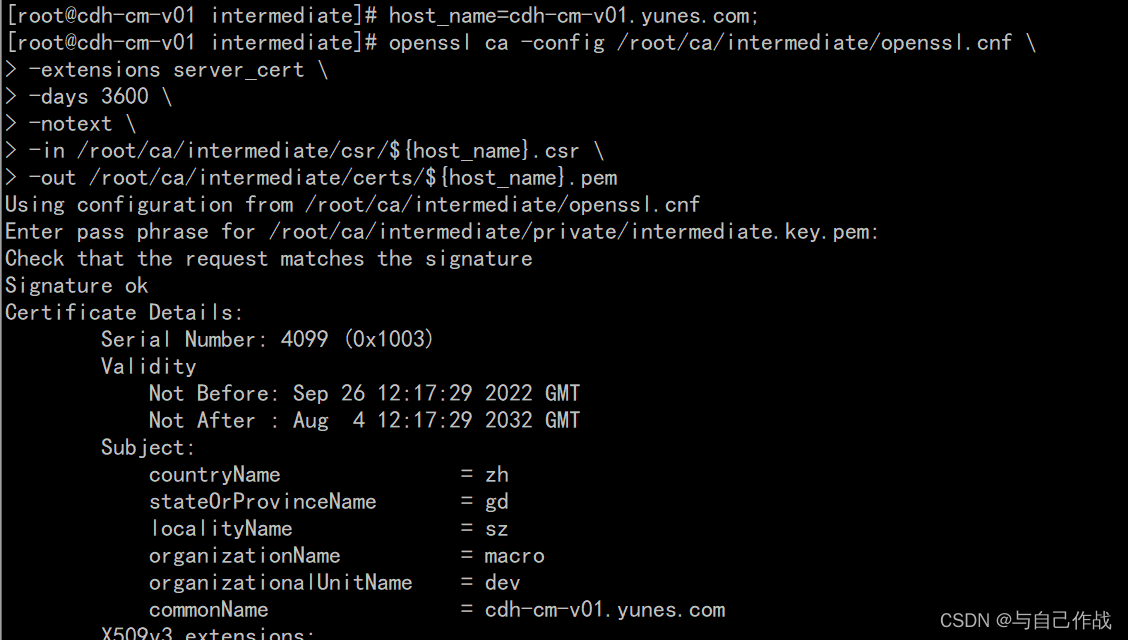
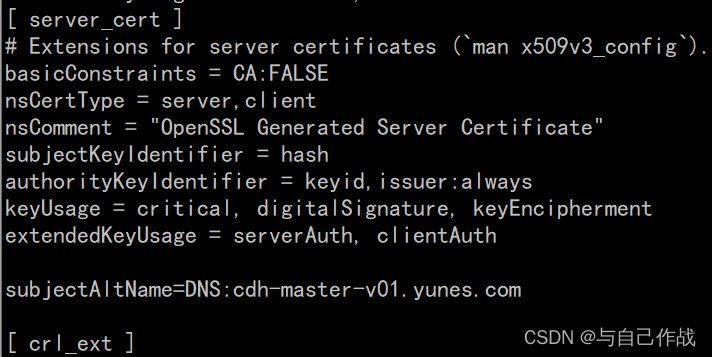
- 注意,图片红框标记的名称cdh-cm-v01.yunes.com必须一致
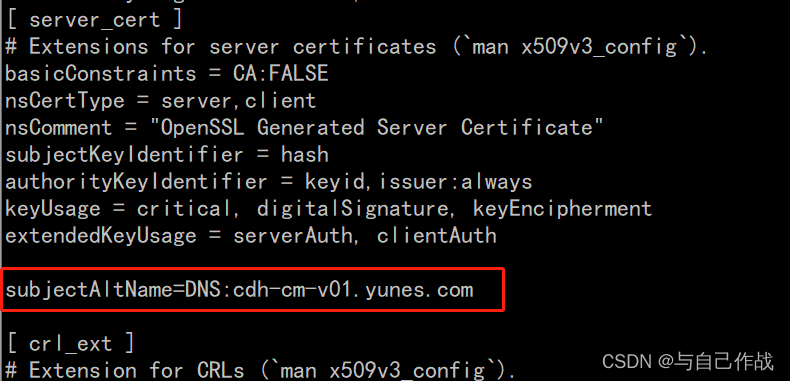
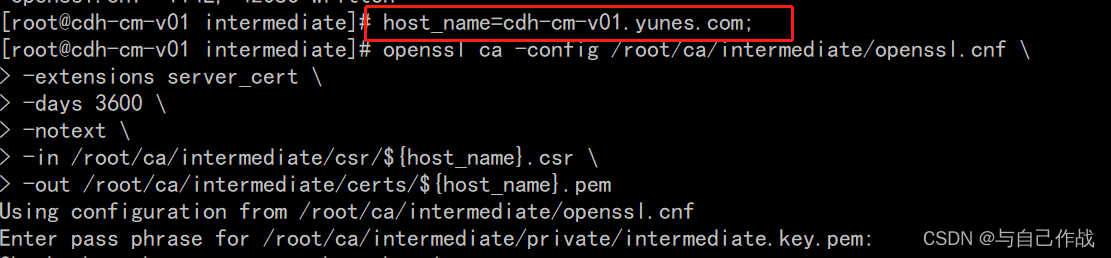
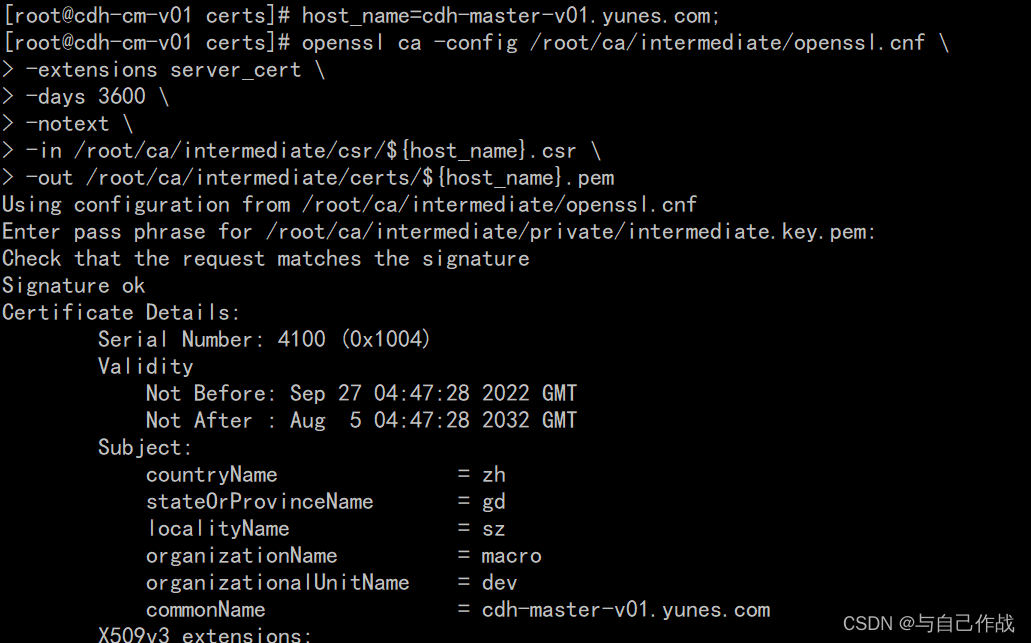
2)其它节点CSR生成操作
vi /root/ca/intermediate/openssl.cnf
[root@cdh-cm-v01 certs]# vi /root/ca/intermediate/openssl.cnf
[ ca ]
# `man ca`
default_ca = CA_default
[ CA_default ]
# Directory and file locations.
dir = /root/ca/intermediate
certs = $dir/certs
crl_dir = $dir/crl
new_certs_dir = $dir/newcerts
database = $dir/index.txt
serial = $dir/serial
RANDFILE = $dir/private/.rand
# The root key and root certificate.
private_key = $dir/private/intermediate.key.pem
certificate = $dir/certs/intermediate.cert.pem
# For certificate revocation lists.
crlnumber = $dir/crlnumber
crl = $dir/crl/intermediate.crl.pem
crl_extensions = crl_ext
default_crl_days = 30
# SHA-1 is deprecated, so use SHA-2 instead.
default_md = sha256
name_opt = ca_default
cert_opt = ca_default
default_days = 375
preserve = no
policy = policy_loose
[ policy_strict ]
# The root CA should only sign intermediate certificates that match.
# See the POLICY FORMAT section of `man ca`.
"~/ca/intermediate/openssl.cnf" 114L, 4212C
[root@cdh-cm-v01 certs]# host_name=cdh-master-v01.yunes.com;
[root@cdh-cm-v01 certs]# openssl ca -config /root/ca/intermediate/openssl.cnf \
> -extensions server_cert \
> -days 3600 \
> -notext \
> -in /root/ca/intermediate/csr/${host_name}.csr \
> -out /root/ca/intermediate/certs/${host_name}.pem
Using configuration from /root/ca/intermediate/openssl.cnf
Enter pass phrase for /root/ca/intermediate/private/intermediate.key.pem:
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number: 4100 (0x1004)
Validity
Not Before: Sep 27 04:47:28 2022 GMT
Not After : Aug 5 04:47:28 2032 GMT
Subject:
countryName = zh
stateOrProvinceName = gd
localityName = sz
organizationName = macro
organizationalUnitName = dev
commonName = cdh-master-v01.yunes.com
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Cert Type:
SSL Client, SSL Server
Netscape Comment:
OpenSSL Generated Server Certificate
X509v3 Subject Key Identifier:
CF:D7:25:A3:9E:14:EF:78:A3:5D:61:DD:8E:19:C5:91:AF:31:37:67
X509v3 Authority Key Identifier:
keyid:AC:52:5E:07:72:71:85:56:01:CF:53:1F:5A:60:A4:1B:82:F4:6B:F1
DirName:/C=zh/ST=gd/L=sz/O=yunes/OU=yunes/CN=yunes/emailAddress=gsxxx@163.com
serial:10:00
X509v3 Key Usage: critical
Digital Signature, Key Encipherment
X509v3 Extended Key Usage:
TLS Web Server Authentication, TLS Web Client Authentication
X509v3 Subject Alternative Name:
DNS:cdh-master-v01.yunes.com
Certificate is to be certified until Aug 5 04:47:28 2032 GMT (3600 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified, commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
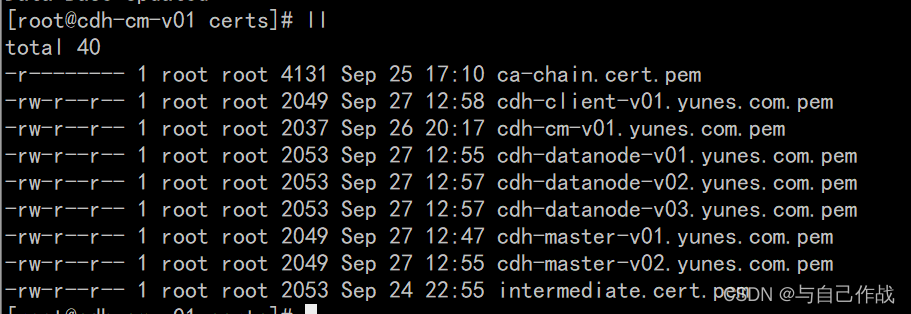
3)最终查询结果
ll
[root@cdh-cm-v01 certs]# ll
total 40
-r-------- 1 root root 4131 Sep 25 17:10 ca-chain.cert.pem
-rw-r--r-- 1 root root 2049 Sep 27 12:58 cdh-client-v01.yunes.com.pem
-rw-r--r-- 1 root root 2037 Sep 26 20:17 cdh-cm-v01.yunes.com.pem
-rw-r--r-- 1 root root 2053 Sep 27 12:55 cdh-datanode-v01.yunes.com.pem
-rw-r--r-- 1 root root 2053 Sep 27 12:57 cdh-datanode-v02.yunes.com.pem
-rw-r--r-- 1 root root 2053 Sep 27 12:57 cdh-datanode-v03.yunes.com.pem
-rw-r--r-- 1 root root 2049 Sep 27 12:47 cdh-master-v01.yunes.com.pem
-rw-r--r-- 1 root root 2049 Sep 27 12:55 cdh-master-v02.yunes.com.pem
-rw-r--r-- 1 root root 2053 Sep 24 22:55 intermediate.cert.pem
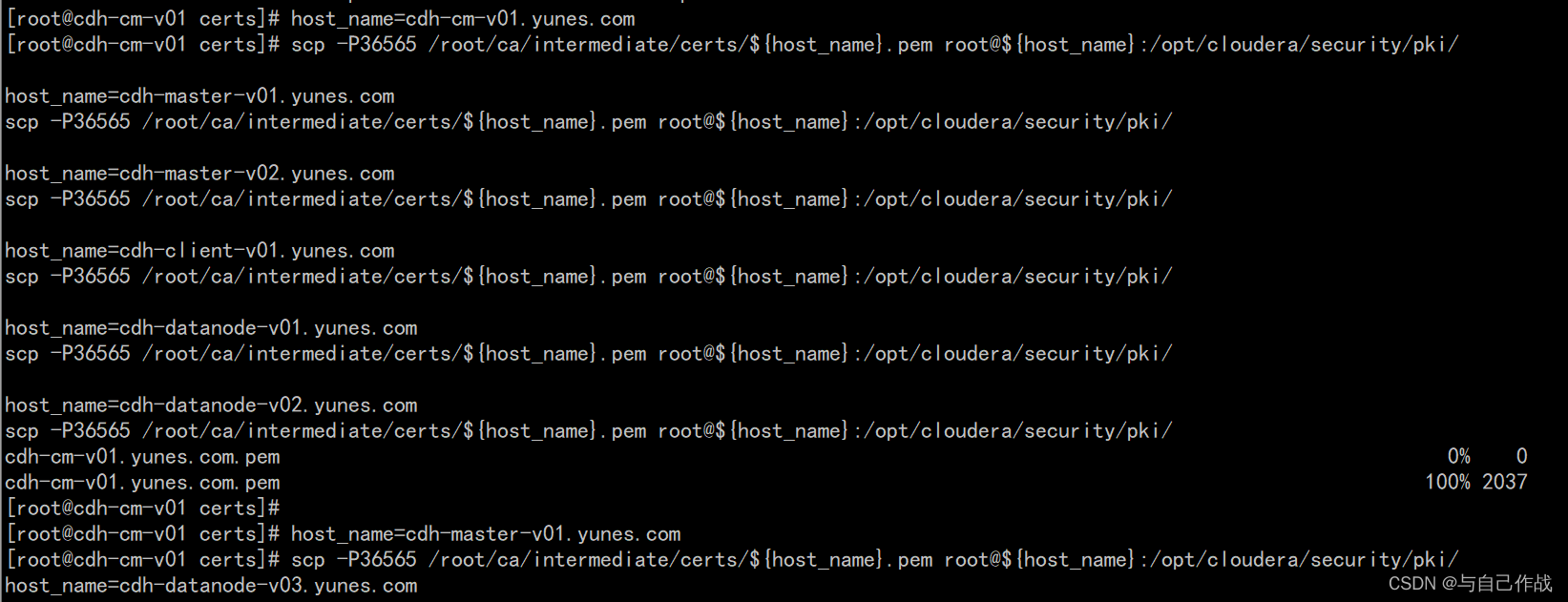
6、将SRC certificate发送回对应的节点
host_name=cdh-cm-v01.yunes.com
scp -P36565 /root/ca/intermediate/certs/ h o s t n a m e . p e m r o o t @ {host_name}.pem root@ hostname.pemroot@{host_name}:/opt/cloudera/security/pki/
host_name=cdh-master-v01.yunes.com
scp -P36565 /root/ca/intermediate/certs/ h o s t n a m e . p e m r o o t @ {host_name}.pem root@ hostname.pemroot@{host_name}:/opt/cloudera/security/pki/
host_name=cdh-master-v02.yunes.com
scp -P36565 /root/ca/intermediate/certs/ h o s t n a m e . p e m r o o t @ {host_name}.pem root@ hostname.pemroot@{host_name}:/opt/cloudera/security/pki/
host_name=cdh-client-v01.yunes.com
scp -P36565 /root/ca/intermediate/certs/ h o s t n a m e . p e m r o o t @ {host_name}.pem root@ hostname.pemroot@{host_name}:/opt/cloudera/security/pki/
host_name=cdh-datanode-v01.yunes.com
scp -P36565 /root/ca/intermediate/certs/ h o s t n a m e . p e m r o o t @ {host_name}.pem root@ hostname.pemroot@{host_name}:/opt/cloudera/security/pki/
host_name=cdh-datanode-v02.yunes.com
scp -P36565 /root/ca/intermediate/certs/ h o s t n a m e . p e m r o o t @ {host_name}.pem root@ hostname.pemroot@{host_name}:/opt/cloudera/security/pki/
host_name=cdh-datanode-v03.yunes.com
scp -P36565 /root/ca/intermediate/certs/ h o s t n a m e . p e m r o o t @ {host_name}.pem root@ hostname.pemroot@{host_name}:/opt/cloudera/security/pki/
[root@cdh-cm-v01 certs]# host_name=cdh-cm-v01.yunes.com
[root@cdh-cm-v01 certs]# scp -P36565 /root/ca/intermediate/certs/${host_name}.pem root@${host_name}:/opt/cloudera/security/pki/
host_name=cdh-master-v01.yunes.com
scp -P36565 /root/ca/intermediate/certs/${host_name}.pem root@${host_name}:/opt/cloudera/security/pki/
host_name=cdh-master-v02.yunes.com
scp -P36565 /root/ca/intermediate/certs/${host_name}.pem root@${host_name}:/opt/cloudera/security/pki/
host_name=cdh-client-v01.yunes.com
scp -P36565 /root/ca/intermediate/certs/${host_name}.pem root@${host_name}:/opt/cloudera/security/pki/
host_name=cdh-datanode-v01.yunes.com
scp -P36565 /root/ca/intermediate/certs/${host_name}.pem root@${host_name}:/opt/cloudera/security/pki/
host_name=cdh-datanode-v02.yunes.com
scp -P36565 /root/ca/intermediate/certs/${host_name}.pem root@${host_name}:/opt/cloudera/security/pki/
cdh-cm-v01.yunes.com.pem 0% 0 0.0KB/s --:-- ETA
cdh-cm-v01.yunes.com.pem 100% 2037 2.3MB/s 00:00
[root@cdh-cm-v01 certs]#
[root@cdh-cm-v01 certs]# host_name=cdh-master-v01.yunes.com
[root@cdh-cm-v01 certs]# scp -P36565 /root/ca/intermediate/certs/${host_name}.pem root@${host_name}:/opt/cloudera/security/pki/
host_name=cdh-datanode-v03.yunes.com
cdh-master-v01.yunes.com.pem 100% 2049 2.0MB/s 00:00
[root@cdh-cm-v01 certs]#
[root@cdh-cm-v01 certs]# host_name=cdh-master-v02.yunes.com
[root@cdh-cm-v01 certs]# scp -P36565 /root/ca/intermediate/certs/${host_name}.pem root@${host_name}:/opt/cloudera/security/pki/
cdh-master-v02.yunes.com.pem 100% 2049 1.7MB/s 00:00
[root@cdh-cm-v01 certs]#
[root@cdh-cm-v01 certs]# host_name=cdh-client-v01.yunes.com
[root@cdh-cm-v01 certs]# scp -P36565 /root/ca/intermediate/certs/${host_name}.pem root@${host_name}:/opt/cloudera/security/pki/
cdh-client-v01.yunes.com.pem 100% 2049 1.9MB/s 00:00
[root@cdh-cm-v01 certs]#
[root@cdh-cm-v01 certs]# host_name=cdh-datanode-v01.yunes.com
[root@cdh-cm-v01 certs]# scp -P36565 /root/ca/intermediate/certs/${host_name}.pem root@${host_name}:/opt/cloudera/security/pki/
cdh-datanode-v01.yunes.com.pem 100% 2053 2.1MB/s 00:00
[root@cdh-cm-v01 certs]#
[root@cdh-cm-v01 certs]# host_name=cdh-datanode-v02.yunes.com
[root@cdh-cm-v01 certs]# scp -P36565 /root/ca/intermediate/certs/${host_name}.pem root@${host_name}:/opt/cloudera/security/pki/
cdh-datanode-v02.yunes.com.pem 100% 2053 2.4MB/s 00:00
[root@cdh-cm-v01 certs]#
[root@cdh-cm-v01 certs]# host_name=cdh-datanode-v03.yunes.com
[root@cdh-cm-v01 certs]# scp -P36565 /root/ca/intermediate/certs/${host_name}.pem root@${host_name}:/opt/cloudera/security/pki/
cdh-datanode-v03.yunes.com.pem 100% 2053 2.2MB/s 00:00
[root@cdh-cm-v01 certs]#
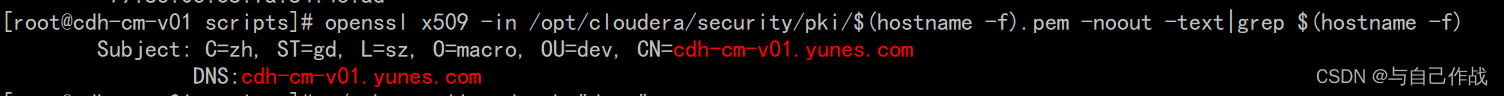
7、验证(所有节点)
openssl x509 -in /opt/cloudera/security/pki/$(hostname -f).pem -noout -text|grep $(hostname -f)
[root@cdh-cm-v01 scripts]# openssl x509 -in /opt/cloudera/security/pki/$(hostname -f).pem -noout -text|grep $(hostname -f)
Subject: C=zh, ST=gd, L=sz, O=macro, OU=dev, CN=cdh-cm-v01.yunes.com
DNS:cdh-cm-v01.yunes.com
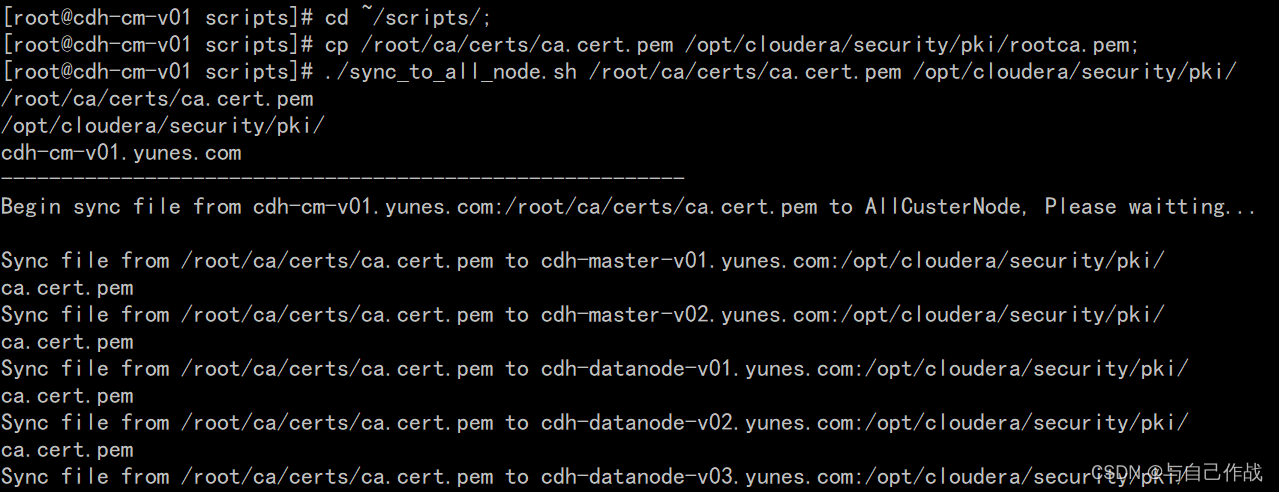
8、拷贝CA certificates到所有节点,并重命名
1)拷贝root CA certificates到所有节点,并重命名为rootca.pem
cd ~/scripts/;
cp /root/ca/certs/ca.cert.pem /opt/cloudera/security/pki/rootca.pem;
./sync_to_all_node.sh /root/ca/certs/ca.cert.pem /opt/cloudera/security/pki/
./ssh_to_all_node.sh “cd /opt/cloudera/security/pki/; mv ca.cert.pem rootca.pem;”
./ssh_to_all_node.sh “ls /opt/cloudera/security/pki/rootca.pem”
[root@cdh-cm-v01 scripts]# cd ~/scripts/;
[root@cdh-cm-v01 scripts]# cp /root/ca/certs/ca.cert.pem /opt/cloudera/security/pki/rootca.pem;
[root@cdh-cm-v01 scripts]# ./sync_to_all_node.sh /root/ca/certs/ca.cert.pem /opt/cloudera/security/pki/
/root/ca/certs/ca.cert.pem
/opt/cloudera/security/pki/
cdh-cm-v01.yunes.com
---------------------------------------------------------
Begin sync file from cdh-cm-v01.yunes.com:/root/ca/certs/ca.cert.pem to AllCusterNode, Please waitting...
Sync file from /root/ca/certs/ca.cert.pem to cdh-master-v01.yunes.com:/opt/cloudera/security/pki/
ca.cert.pem 100% 2078 2.2MB/s 00:00
Sync file from /root/ca/certs/ca.cert.pem to cdh-master-v02.yunes.com:/opt/cloudera/security/pki/
ca.cert.pem 100% 2078 2.3MB/s 00:00
Sync file from /root/ca/certs/ca.cert.pem to cdh-datanode-v01.yunes.com:/opt/cloudera/security/pki/
ca.cert.pem 100% 2078 2.1MB/s 00:00
Sync file from /root/ca/certs/ca.cert.pem to cdh-datanode-v02.yunes.com:/opt/cloudera/security/pki/
ca.cert.pem 100% 2078 2.1MB/s 00:00
Sync file from /root/ca/certs/ca.cert.pem to cdh-datanode-v03.yunes.com:/opt/cloudera/security/pki/
ca.cert.pem 100% 2078 2.1MB/s 00:00
Sync file from /root/ca/certs/ca.cert.pem to cdh-client-v01.yunes.com:/opt/cloudera/security/pki/
ca.cert.pem 100% 2078 2.2MB/s 00:00
[root@cdh-cm-v01 scripts]# ./ssh_to_all_node.sh "cd /opt/cloudera/security/pki/; mv ca.cert.pem rootca.pem;"
cdh-cm-v01.yunes.com
---------------------------------------------------------
Begin run command: [ cd /opt/cloudera/security/pki/; mv ca.cert.pem rootca.pem; ] to AllCusterNode, Please waitting...
Run Command: ssh root@cdh-master-v01.yunes.com cd /opt/cloudera/security/pki/; mv ca.cert.pem rootca.pem;
Run Command: ssh root@cdh-master-v02.yunes.com cd /opt/cloudera/security/pki/; mv ca.cert.pem rootca.pem;
Run Command: ssh root@cdh-datanode-v01.yunes.com cd /opt/cloudera/security/pki/; mv ca.cert.pem rootca.pem;
Run Command: ssh root@cdh-datanode-v02.yunes.com cd /opt/cloudera/security/pki/; mv ca.cert.pem rootca.pem;
Run Command: ssh root@cdh-datanode-v03.yunes.com cd /opt/cloudera/security/pki/; mv ca.cert.pem rootca.pem;
Run Command: ssh root@cdh-client-v01.yunes.com cd /opt/cloudera/security/pki/; mv ca.cert.pem rootca.pem;
[root@cdh-cm-v01 scripts]# ./ssh_to_all_node.sh "ls /opt/cloudera/security/pki/rootca.pem"
cdh-cm-v01.yunes.com
---------------------------------------------------------
Begin run command: [ ls /opt/cloudera/security/pki/rootca.pem ] to AllCusterNode, Please waitting...
Run Command: ssh root@cdh-master-v01.yunes.com ls /opt/cloudera/security/pki/rootca.pem
/opt/cloudera/security/pki/rootca.pem
Run Command: ssh root@cdh-master-v02.yunes.com ls /opt/cloudera/security/pki/rootca.pem
/opt/cloudera/security/pki/rootca.pem
Run Command: ssh root@cdh-datanode-v01.yunes.com ls /opt/cloudera/security/pki/rootca.pem
/opt/cloudera/security/pki/rootca.pem
Run Command: ssh root@cdh-datanode-v02.yunes.com ls /opt/cloudera/security/pki/rootca.pem
/opt/cloudera/security/pki/rootca.pem
Run Command: ssh root@cdh-datanode-v03.yunes.com ls /opt/cloudera/security/pki/rootca.pem
/opt/cloudera/security/pki/rootca.pem
Run Command: ssh root@cdh-client-v01.yunes.com ls /opt/cloudera/security/pki/rootca.pem
/opt/cloudera/security/pki/rootca.pem
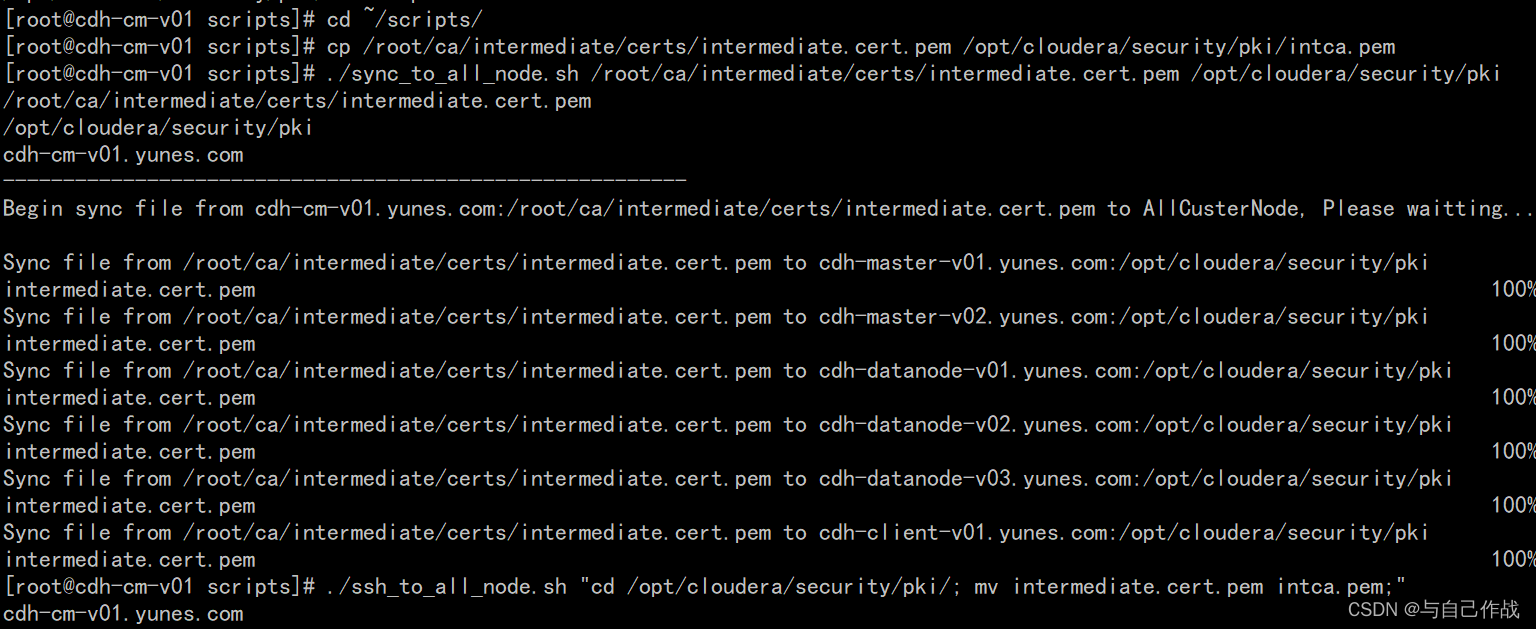
2)拷贝intermediate CA certificates到所有节点,并重命名为intca.pem
cd ~/scripts/;
cp /root/ca/intermediate/certs/intermediate.cert.pem /opt/cloudera/security/pki/intca.pem;
./sync_to_all_node.sh /root/ca/intermediate/certs/intermediate.cert.pem /opt/cloudera/security/pki
./ssh_to_all_node.sh “cd /opt/cloudera/security/pki/; mv intermediate.cert.pem intca.pem;”
./ssh_to_all_node.sh “ls /opt/cloudera/security/pki/intca.pem”
[root@cdh-cm-v01 scripts]# cd ~/scripts/
[root@cdh-cm-v01 scripts]# cp /root/ca/intermediate/certs/intermediate.cert.pem /opt/cloudera/security/pki/intca.pem
[root@cdh-cm-v01 scripts]# ./sync_to_all_node.sh /root/ca/intermediate/certs/intermediate.cert.pem /opt/cloudera/security/pki
/root/ca/intermediate/certs/intermediate.cert.pem
/opt/cloudera/security/pki
cdh-cm-v01.yunes.com
---------------------------------------------------------
Begin sync file from cdh-cm-v01.yunes.com:/root/ca/intermediate/certs/intermediate.cert.pem to AllCusterNode, Please waitting...
Sync file from /root/ca/intermediate/certs/intermediate.cert.pem to cdh-master-v01.yunes.com:/opt/cloudera/security/pki
intermediate.cert.pem 100% 2053 2.4MB/s 00:00
Sync file from /root/ca/intermediate/certs/intermediate.cert.pem to cdh-master-v02.yunes.com:/opt/cloudera/security/pki
intermediate.cert.pem 100% 2053 2.3MB/s 00:00
Sync file from /root/ca/intermediate/certs/intermediate.cert.pem to cdh-datanode-v01.yunes.com:/opt/cloudera/security/pki
intermediate.cert.pem 100% 2053 2.0MB/s 00:00
Sync file from /root/ca/intermediate/certs/intermediate.cert.pem to cdh-datanode-v02.yunes.com:/opt/cloudera/security/pki
intermediate.cert.pem 100% 2053 2.5MB/s 00:00
Sync file from /root/ca/intermediate/certs/intermediate.cert.pem to cdh-datanode-v03.yunes.com:/opt/cloudera/security/pki
intermediate.cert.pem 100% 2053 2.3MB/s 00:00
Sync file from /root/ca/intermediate/certs/intermediate.cert.pem to cdh-client-v01.yunes.com:/opt/cloudera/security/pki
intermediate.cert.pem 100% 2053 1.9MB/s 00:00
[root@cdh-cm-v01 scripts]# ./ssh_to_all_node.sh "cd /opt/cloudera/security/pki/; mv intermediate.cert.pem intca.pem;"
cdh-cm-v01.yunes.com
---------------------------------------------------------
Begin run command: [ cd /opt/cloudera/security/pki/; mv intermediate.cert.pem intca.pem; ] to AllCusterNode, Please waitting...
Run Command: ssh root@cdh-master-v01.yunes.com cd /opt/cloudera/security/pki/; mv intermediate.cert.pem intca.pem;
Run Command: ssh root@cdh-master-v02.yunes.com cd /opt/cloudera/security/pki/; mv intermediate.cert.pem intca.pem;
Run Command: ssh root@cdh-datanode-v01.yunes.com cd /opt/cloudera/security/pki/; mv intermediate.cert.pem intca.pem;
Run Command: ssh root@cdh-datanode-v02.yunes.com cd /opt/cloudera/security/pki/; mv intermediate.cert.pem intca.pem;
Run Command: ssh root@cdh-datanode-v03.yunes.com cd /opt/cloudera/security/pki/; mv intermediate.cert.pem intca.pem;
Run Command: ssh root@cdh-client-v01.yunes.com cd /opt/cloudera/security/pki/; mv intermediate.cert.pem intca.pem;
[root@cdh-cm-v01 scripts]# ./ssh_to_all_node.sh "ls /opt/cloudera/security/pki/intca.pem"
cdh-cm-v01.yunes.com
---------------------------------------------------------
Begin run command: [ ls /opt/cloudera/security/pki/intca.pem ] to AllCusterNode, Please waitting...
Run Command: ssh root@cdh-master-v01.yunes.com ls /opt/cloudera/security/pki/intca.pem
/opt/cloudera/security/pki/intca.pem
Run Command: ssh root@cdh-master-v02.yunes.com ls /opt/cloudera/security/pki/intca.pem
/opt/cloudera/security/pki/intca.pem
Run Command: ssh root@cdh-datanode-v01.yunes.com ls /opt/cloudera/security/pki/intca.pem
/opt/cloudera/security/pki/intca.pem
Run Command: ssh root@cdh-datanode-v02.yunes.com ls /opt/cloudera/security/pki/intca.pem
/opt/cloudera/security/pki/intca.pem
Run Command: ssh root@cdh-datanode-v03.yunes.com ls /opt/cloudera/security/pki/intca.pem
/opt/cloudera/security/pki/intca.pem
Run Command: ssh root@cdh-client-v01.yunes.com ls /opt/cloudera/security/pki/intca.pem
/opt/cloudera/security/pki/intca.pem
[root@cdh-cm-v01 scripts]#
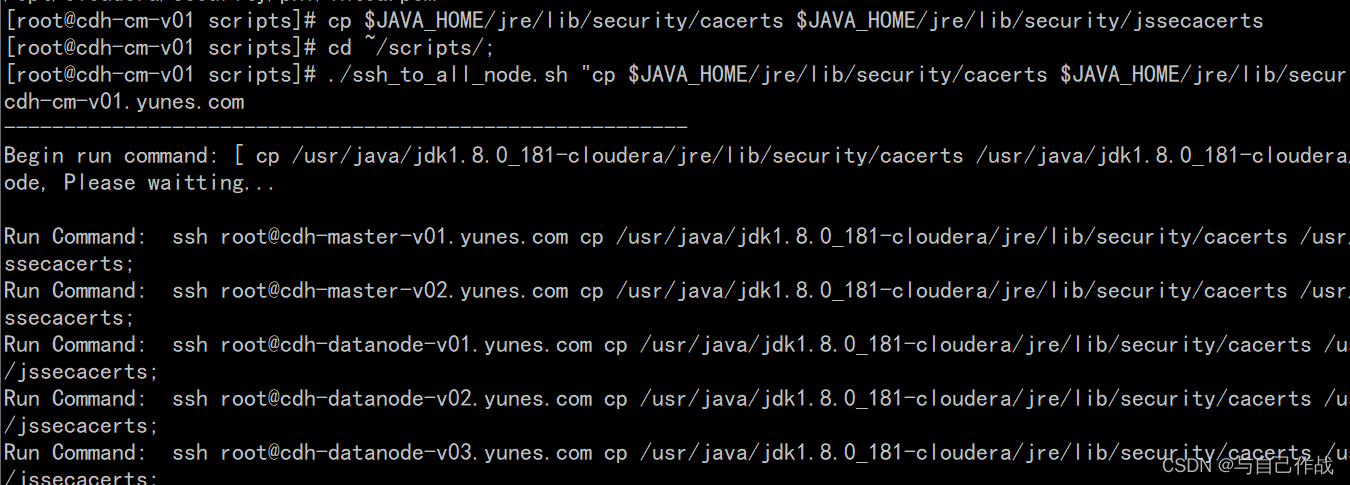
9、将JDK的cacerts文件拷贝到jssecacerts
cp $JAVA_HOME/jre/lib/security/cacerts $JAVA_HOME/jre/lib/security/jssecacerts
cd ~/scripts/;
./ssh_to_all_node.sh “cp $JAVA_HOME/jre/lib/security/cacerts $JAVA_HOME/jre/lib/security/jssecacerts;”
[root@cdh-cm-v01 scripts]# cp $JAVA_HOME/jre/lib/security/cacerts $JAVA_HOME/jre/lib/security/jssecacerts
[root@cdh-cm-v01 scripts]# cd ~/scripts/;
[root@cdh-cm-v01 scripts]# ./ssh_to_all_node.sh "cp $JAVA_HOME/jre/lib/security/cacerts $JAVA_HOME/jre/lib/security/jssecacerts;"
cdh-cm-v01.yunes.com
---------------------------------------------------------
Begin run command: [ cp /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/cacerts /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts; ] to AllCusterNode, Please waitting...
Run Command: ssh root@cdh-master-v01.yunes.com cp /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/cacerts /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts;
Run Command: ssh root@cdh-master-v02.yunes.com cp /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/cacerts /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts;
Run Command: ssh root@cdh-datanode-v01.yunes.com cp /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/cacerts /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts;
Run Command: ssh root@cdh-datanode-v02.yunes.com cp /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/cacerts /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts;
Run Command: ssh root@cdh-datanode-v03.yunes.com cp /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/cacerts /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts;
Run Command: ssh root@cdh-client-v01.yunes.com cp /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/cacerts /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts;
[root@cdh-cm-v01 scripts]# ./ssh_to_all_node.sh "ls -l $JAVA_HOME/jre/lib/security/jssecacerts"
cdh-cm-v01.yunes.com
---------------------------------------------------------
Begin run command: [ ls -l /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts ] to AllCusterNode, Please waitting...
Run Command: ssh root@cdh-master-v01.yunes.com ls -l /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts
-rw-r--r-- 1 root root 114757 Sep 27 14:52 /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts
Run Command: ssh root@cdh-master-v02.yunes.com ls -l /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts
-rw-r--r-- 1 root root 114757 Sep 27 14:52 /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts
Run Command: ssh root@cdh-datanode-v01.yunes.com ls -l /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts
-rw-r--r-- 1 root root 114757 Sep 27 15:15 /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts
Run Command: ssh root@cdh-datanode-v02.yunes.com ls -l /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts
-rw-r--r-- 1 root root 114757 Sep 27 15:15 /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts
Run Command: ssh root@cdh-datanode-v03.yunes.com ls -l /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts
-rw-r--r-- 1 root root 114757 Sep 27 15:15 /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts
Run Command: ssh root@cdh-client-v01.yunes.com ls -l /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts
-rw-r--r-- 1 root root 114757 Sep 27 15:15 /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts
[root@cdh-cm-v01 scripts]# ls -l $JAVA_HOME/jre/lib/security/jssecacerts
-rw-r--r-- 1 root root 114757 Sep 27 15:15 /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts
[root@cdh-cm-v01 scripts]# ll $JAVA_HOME/jre/lib/security/jssecacerts
-rw-r--r-- 1 root root 114757 Sep 27 15:15 /usr/java/jdk1.8.0_181-cloudera/jre/lib/security/jssecacerts
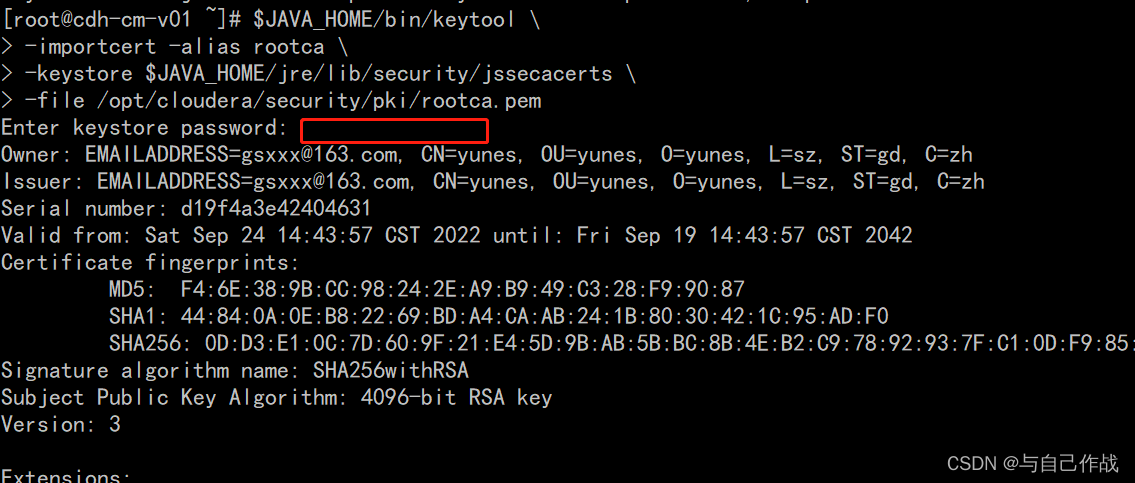
10、将root CA certificate导入到jssecacerts当中(所有机器)
$JAVA_HOME/bin/keytool
-importcert -alias rootca
-keystore $JAVA_HOME/jre/lib/security/jssecacerts
-file /opt/cloudera/security/pki/rootca.pem
[root@cdh-cm-v01 ~]# $JAVA_HOME/bin/keytool \
> -importcert -alias rootca \
> -keystore $JAVA_HOME/jre/lib/security/jssecacerts \
> -file /opt/cloudera/security/pki/rootca.pem
Enter keystore password: changeit
Owner: EMAILADDRESS=gsxxx@163.com, CN=yunes, OU=yunes, O=yunes, L=sz, ST=gd, C=zh
Issuer: EMAILADDRESS=gsxxx@163.com, CN=yunes, OU=yunes, O=yunes, L=sz, ST=gd, C=zh
Serial number: d19f4a3e42404631
Valid from: Sat Sep 24 14:43:57 CST 2022 until: Fri Sep 19 14:43:57 CST 2042
Certificate fingerprints:
MD5: F4:6E:38:9B:CC:98:24:2E:A9:B9:49:C3:28:F9:90:87
SHA1: 44:84:0A:0E:B8:22:69:BD:A4:CA:AB:24:1B:80:30:42:1C:95:AD:F0
SHA256: 0D:D3:E1:0C:7D:60:9F:21:E4:5D:9B:AB:5B:BC:8B:4E:B2:C9:78:92:93:7F:C1:0D:F9:85:4C:D0:C9:9E:05:8C
Signature algorithm name: SHA256withRSA
Subject Public Key Algorithm: 4096-bit RSA key
Version: 3
Extensions:
#1: ObjectId: 2.5.29.35 Criticality=false
AuthorityKeyIdentifier [
KeyIdentifier [
0000: 52 2D 7C 48 AE 04 3B 71 50 53 38 61 5B 11 04 39 R-.H..;qPS8a[..9
0010: 63 CD 83 8A c...
]
]
#2: ObjectId: 2.5.29.19 Criticality=true
BasicConstraints:[
CA:true
PathLen:2147483647
]
#3: ObjectId: 2.5.29.15 Criticality=true
KeyUsage [
DigitalSignature
Key_CertSign
Crl_Sign
]
#4: ObjectId: 2.5.29.14 Criticality=false
SubjectKeyIdentifier [
KeyIdentifier [
0000: 52 2D 7C 48 AE 04 3B 71 50 53 38 61 5B 11 04 39 R-.H..;qPS8a[..9
0010: 63 CD 83 8A c...
]
]
Trust this certificate? [no]: y
Certificate was added to keystore
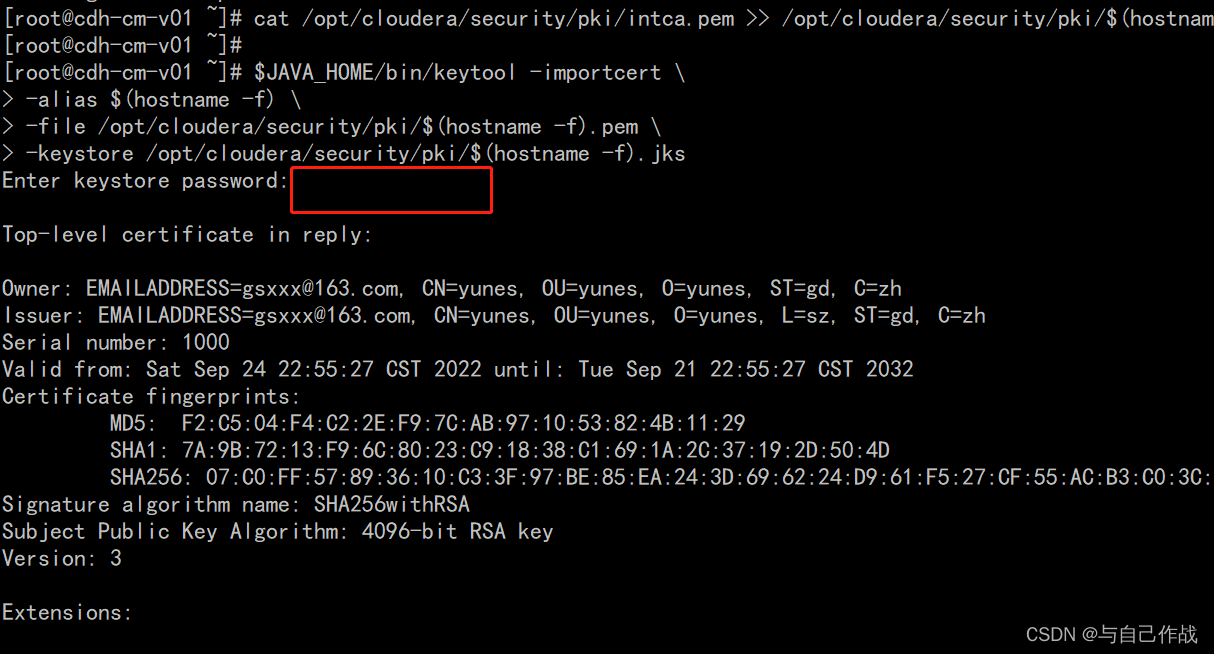
11、将intermediate CA certificate添加到各节点的节点证书中,并将其导入到java keystore中
cat /opt/cloudera/security/pki/intca.pem >> /opt/cloudera/security/pki/$(hostname -f).pem
$JAVA_HOME/bin/keytool -importcert
-alias ( h o s t n a m e − f ) − f i l e / o p t / c l o u d e r a / s e c u r i t y / p k i / (hostname -f) \ -file /opt/cloudera/security/pki/ (hostname−f) −file/opt/cloudera/security/pki/(hostname -f).pem
-keystore /opt/cloudera/security/pki/$(hostname -f).jks
[root@cdh-cm-v01 ~]# cat /opt/cloudera/security/pki/intca.pem >> /opt/cloudera/security/pki/$(hostname -f).pem
[root@cdh-cm-v01 ~]#
[root@cdh-cm-v01 ~]# $JAVA_HOME/bin/keytool -importcert \
> -alias $(hostname -f) \
> -file /opt/cloudera/security/pki/$(hostname -f).pem \
> -keystore /opt/cloudera/security/pki/$(hostname -f).jks
Enter keystore password: tianlingqun
Top-level certificate in reply:
Owner: EMAILADDRESS=gsxxx@163.com, CN=yunes, OU=yunes, O=yunes, ST=gd, C=zh
Issuer: EMAILADDRESS=gsxxx@163.com, CN=yunes, OU=yunes, O=yunes, L=sz, ST=gd, C=zh
Serial number: 1000
Valid from: Sat Sep 24 22:55:27 CST 2022 until: Tue Sep 21 22:55:27 CST 2032
Certificate fingerprints:
MD5: F2:C5:04:F4:C2:2E:F9:7C:AB:97:10:53:82:4B:11:29
SHA1: 7A:9B:72:13:F9:6C:80:23:C9:18:38:C1:69:1A:2C:37:19:2D:50:4D
SHA256: 07:C0:FF:57:89:36:10:C3:3F:97:BE:85:EA:24:3D:69:62:24:D9:61:F5:27:CF:55:AC:B3:C0:3C:1D:F9:B4:6A
Signature algorithm name: SHA256withRSA
Subject Public Key Algorithm: 4096-bit RSA key
Version: 3
Extensions:
#1: ObjectId: 2.5.29.35 Criticality=false
AuthorityKeyIdentifier [
KeyIdentifier [
0000: 52 2D 7C 48 AE 04 3B 71 50 53 38 61 5B 11 04 39 R-.H..;qPS8a[..9
0010: 63 CD 83 8A c...
]
]
#2: ObjectId: 2.5.29.19 Criticality=true
BasicConstraints:[
CA:true
PathLen:0
]
#3: ObjectId: 2.5.29.15 Criticality=true
KeyUsage [
DigitalSignature
Key_CertSign
Crl_Sign
]
#4: ObjectId: 2.5.29.14 Criticality=false
SubjectKeyIdentifier [
KeyIdentifier [
0000: AC 52 5E 07 72 71 85 56 01 CF 53 1F 5A 60 A4 1B .R^.rq.V..S.Z`..
0010: 82 F4 6B F1 ..k.
]
]
... is not trusted. Install reply anyway? [no]: y
Certificate reply was installed in keystore
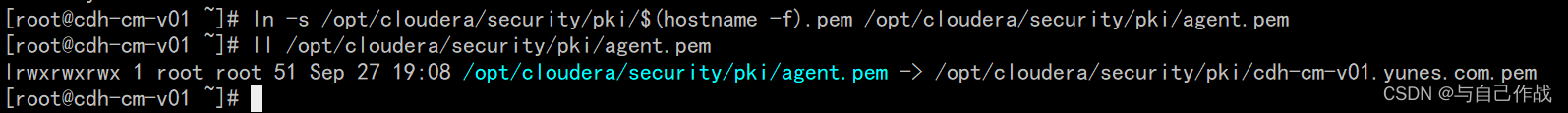
12、创建软连接(所有机器)
ln -s /opt/cloudera/security/pki/$(hostname -f).pem /opt/cloudera/security/pki/agent.pem
[root@cdh-cm-v01 ~]# ln -s /opt/cloudera/security/pki/$(hostname -f).pem /opt/cloudera/security/pki/agent.pem
[root@cdh-cm-v01 ~]# ll /opt/cloudera/security/pki/agent.pem
lrwxrwxrwx 1 root root 51 Sep 27 19:08 /opt/cloudera/security/pki/agent.pem -> /opt/cloudera/security/pki/cdh-cm-v01.yunes.com.pem
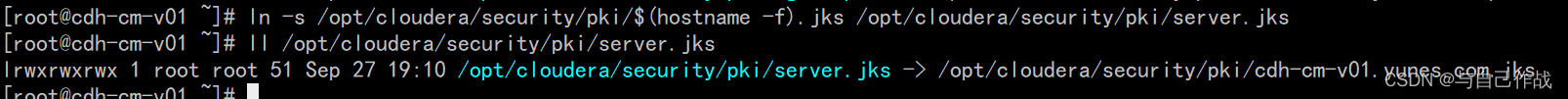
13、创建软连接(cdh-cm-v01)
ln -s /opt/cloudera/security/pki/$(hostname -f).jks /opt/cloudera/security/pki/server.jks
[root@cdh-cm-v01 ~]# ln -s /opt/cloudera/security/pki/$(hostname -f).jks /opt/cloudera/security/pki/server.jks
[root@cdh-cm-v01 ~]# ll /opt/cloudera/security/pki/server.jks
lrwxrwxrwx 1 root root 51 Sep 27 19:10 /opt/cloudera/security/pki/server.jks -> /opt/cloudera/security/pki/cdh-cm-v01.yunes.com.jks